Technical Report
As a black box vulnerability scanner, Invicti crawls and attacks your web application to detect the vulnerable points. Once the scan is finished – and also during the scan – the Invicti dashboard provides you with an overview of the security status of your web application, its vulnerabilities and issues. The Technical Report section of a Invicti Enterprise report offers in-depth information and provides useful shortcuts for immediate action.

- This report displays information about the number, severity, and types of vulnerabilities identified, the impact they could have, and where they exist on the site.
- Further, using this report enables you to access further technical information such as Request and Response codes, and Proof of Exploit or Concept.
- Additionally, you can access Sitemap, Knowledge Base, and the Scan Summary.
- Technical Report also makes it easy for you to take action on detected issues. If you have integrated any issue tracking system (click for more information on Integrations), you can assign issues to developers so that they can work on fixing them. Alternatively, you can easily classify any of these vulnerabilities as Accepted Risks or Fixed.
In Invicti Enterprise, The Issues, Sitemap and Knowledge Base features described in this topic are displayed in the Technical Report.
In Invicti Standard, they are displayed instead in the Panels in the Scan Summary Dashboard.
Issues Tab
The Issues tab lists all identified vulnerabilities and issues. Vulnerabilities are arranged into groups called ‘families’, in which they are prioritized based on their exploitability.
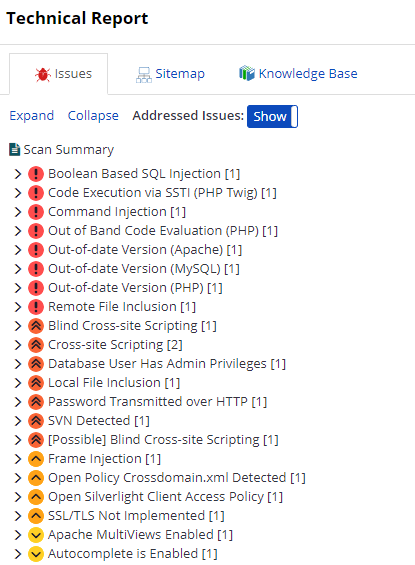
If you click on an identified issue, you are provided with further information, showing whether the issue is Critical or Confirmed. You can also assign this issue to developers using the Send To button. Or, you can update the status of an issue as Fixed or Accepted Risk.
This table lists the sections in the Issue window.
- URL
- [IAST] Source File
- [IAST] Extra Information
- Parameter Name
- Parameter Type
- Attack Pattern
- Retestable
- Vulnerability Details
- Impact
- Actions to Take
- Required Skills for Successful Exploitation
- Remedy
- Remedy Preferences
- External Preferences
- Classification
- CVSS Score
Addressed Issues (Show/Hide): This option allows you to hide issues that are fixed or addressed or to display all issues.
For further information on the Issues panel in Invicti Standard, see Issues.
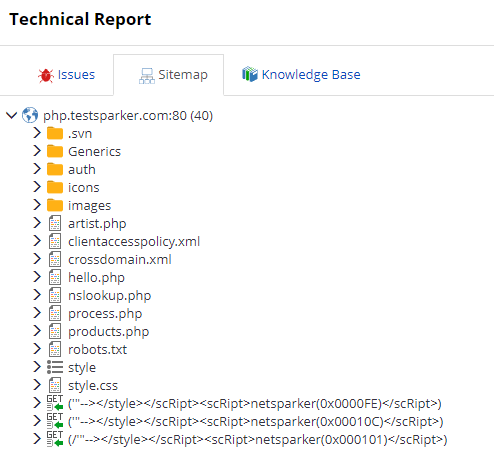
Sitemap Tab
This Sitemap tab displays a list of all the directories and files that the scanner crawled. Within each node, all identified vulnerabilities, security flaws and vulnerable parameters are listed.
Knowledge Base Tab
The Knowledge Base tab displays a list of additional information about the scan and is grouped into, such as the number of proof and links, crawling and scan performance, and slowest pages.
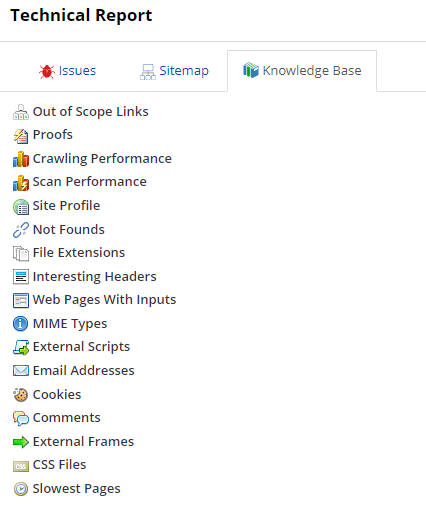
This information is useful for highlighting other potential security issues that are not typically classified as vulnerabilities but can help attackers gain additional knowledge to craft a successful attack. This is one way that Invicti provides users with a complete, detailed analysis of the target web application.
For further information, see Knowledge Base, Knowledge Base nodes, and Knowledge Base Report in the Scan Summary dashboard.
Scan Summary Tab
The Scan Summary tab displays details of the scan, allowing you to see numbers of Issues grouped by severity. It also includes the Request and Response Code, Compliance Summary, and Technologies.
| Scan | This is a list of key information about the scan, such as:
|
| Issues | This is a list of detected issues, classified according to:
For further information, see Viewing Issues in Invicti Enterprise and Viewing Issues in Invicti Standard. |
| Impacts | This shows the level of potential damage that attackers could inflict – such as accessing database or user information – due to vulnerabilities identified in the target web application.
For further information, see Vulnerability Severity Levels |
| Compliance Summary |
This is a list of the issues relevant to:
For further information, see OWASP Top Ten 2013 Report, OWASP Top Ten 2017 Report, PCI DSS Compliance Report and ISO 27001 Compliance Report. |
| Technologies | This shows the technologies used in web applications. Invicti Enterprise tracks and reports on problems, such as whether any of the technologies are out-of-date or whether a specific version has any issues.
For further information, see Technologies. |